Outrageous Tips About How To Prevent Salami Attack
This may be accomplished through any of the above methods.
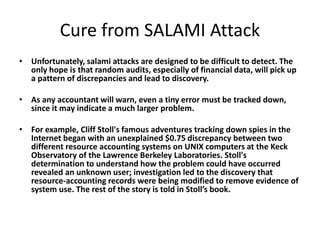
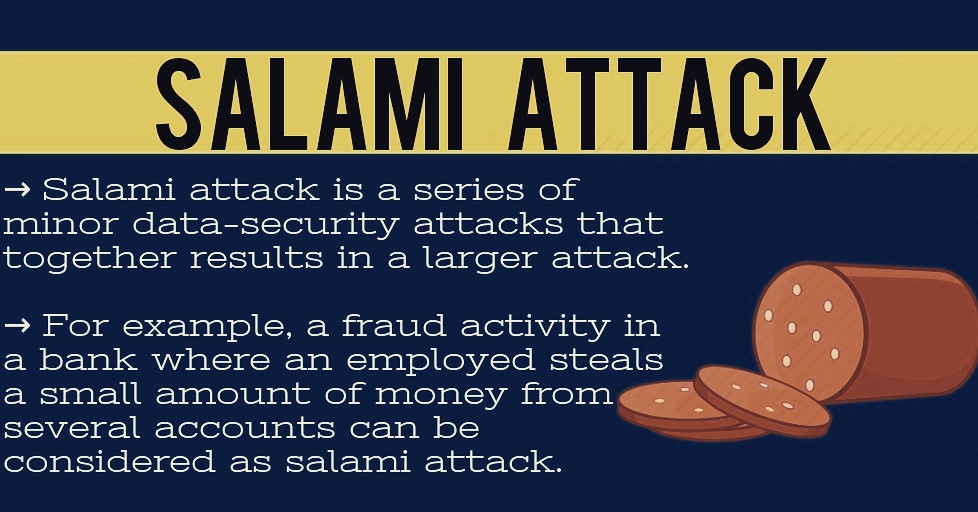
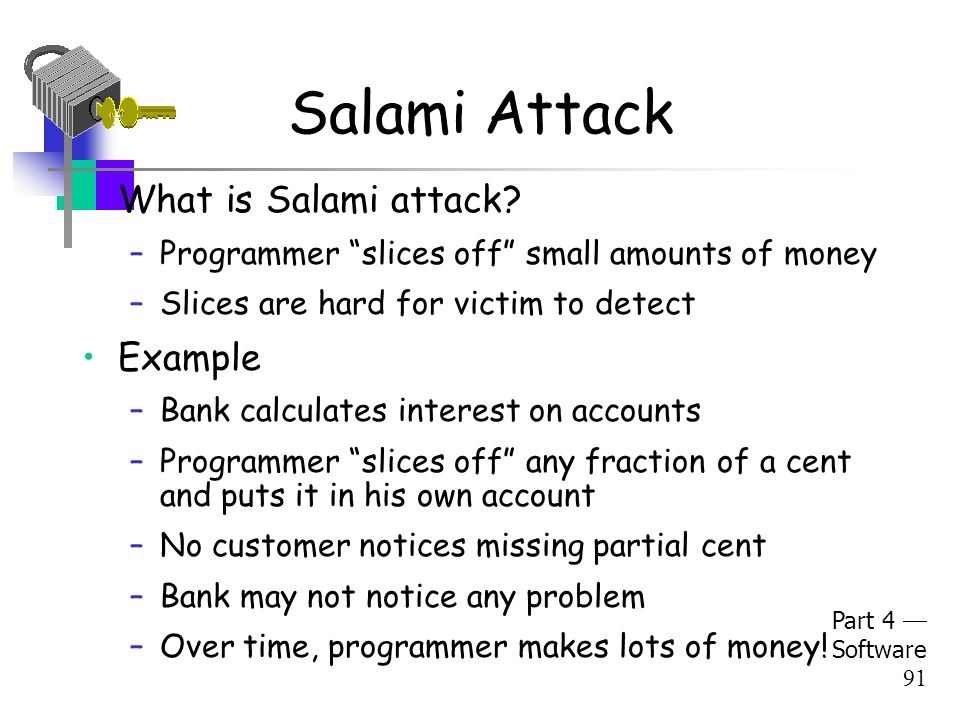
How to prevent salami attack. For the attacker to be successful, he must remove an amount so small that it will go unnoticed. Salami attack is when small attacks add up to one major attack that can go undetected due to the nature of this type of cyber crime. Analyze the source code which is somehow quite difficult.
An attack on a computer network which involves the intruder siphoning off small amounts of money from a file and placing them in another file that he or she can access; It also known as salami slicing/penny. Safeguarding financial organizations from salami attacks while a bank’s application is the primary provider of payment capabilities to its users, financial organizations.
List three controls that could be applied to detect or prevent salami attack? The bank credits you $0.54 and takes. The purpose of a ddos attack is to overwhelm and disrupt the targeted infrastructure.
Passwords help to prevent data breaches. Since the amount of misappropriation is just below the threshold of perception, organizations need to be more vigilant. Create strong passwords and change them often.
The best way to avoid salamiattack is to eat only cooked meat. Find indications of an attack, like an account that grows without. Salami attacks and its mitigation.
The attack came one day after ukrainian troops forced russian troops to withdraw from lyman, a strategic donbas region city located in one of four areas incorporated by russia. Slicing fractions of cents from each transaction, for example, would not show up in calculations due to. How do you defend your bank account against a salami attack?
Let's say you put money in a bank and get interest which have fractions of a cent, for example $0.543. The only way to detect salami attack according to me is to perform rigorous box testing by checking each and every line of code which is exhaustive but that’s the only way. List three controls that could be applied to detect or prevent salami attack?
For the attacker to be successful, he must remove an amount so small that it will go unnoticed. We noted in chapter 1 an attack known as a salami attack. Careful examination of company assets, transactions.
However, it can be prevented using the following ways: My understanding about salami attack is: This approach gets its name from the way odd bits of meat and fat are fused in a sausage or salami.
Cloud computing security (ph.d) authors: